Home » IP and Device Intelligence
IP and Device Intelligence
With ScreenlyyID’s IP and device intelligence check your business can confidently identify fraud patterns quickly, and help detect malware, attack sources, bots and botnets while protecting your customer experience
Gather digital signals to quickly and easily filter out high-risk customers.
Identify suspicious users by detecting harmful IP's, allowing you to distinguish legitimate users from malicious ones.
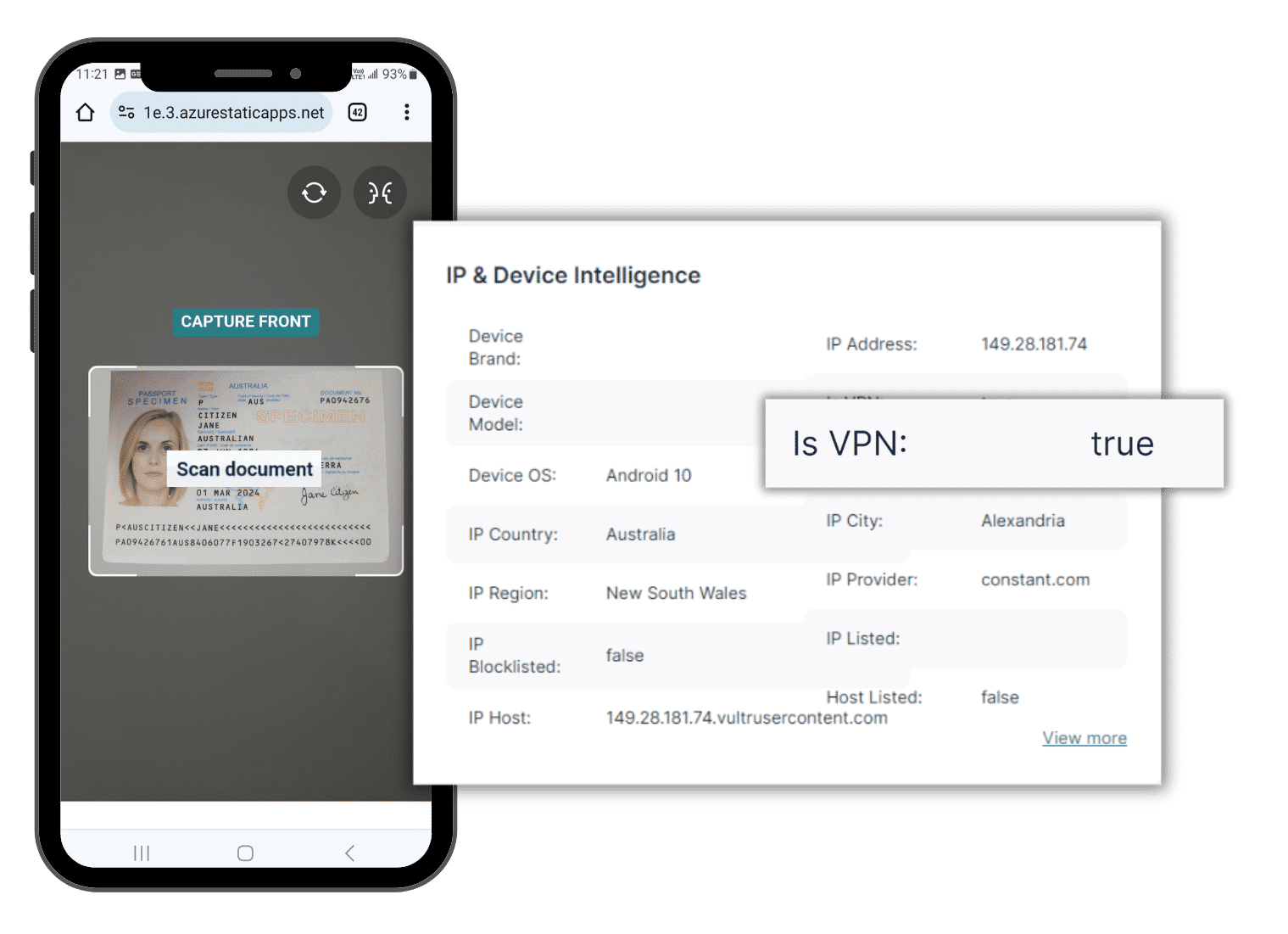
IP & Device intelligence lookup provides detailed insights into a user’s connection, covering VPN/proxy usage, Tor connections, data centers, ISP details, and geolocation. This data enhances risk assessments, evaluates VPN/Tor users, and informs models for KYC, AML processes, iGaming bonus abuse, chargeback prevention, and beyond.
Use device fingerprinting and intelligence to discern high risk device ID.
Detect fake Accounts and filter out high risk applications during digital onboarding.
Identify endpoint threats in applications, such as bots and emulators.
Identify suspicious IP's and VPN's
Retrieve valuable IP address information
Identify the geolocation of an IP address down to the city level, including the geographic coordinates and detailed locale information. Our geolocation database is continuously updated in real time as internet address allocation changes and as new IP ranges come online.
IP Probe
Analyze and extract provider information for a single IP address
IP probe will perform a real time scan against the given IP using various network level checks. We analyze the data retrieved and determine what type of provider the IP belongs to.
ScreenlyyID uses network level service probes to check if the IP is running common VPN or proxy software. IP probe provides excellent detection of VPN and proxy services, which is a key indicator of bots and fraudulent applicants.
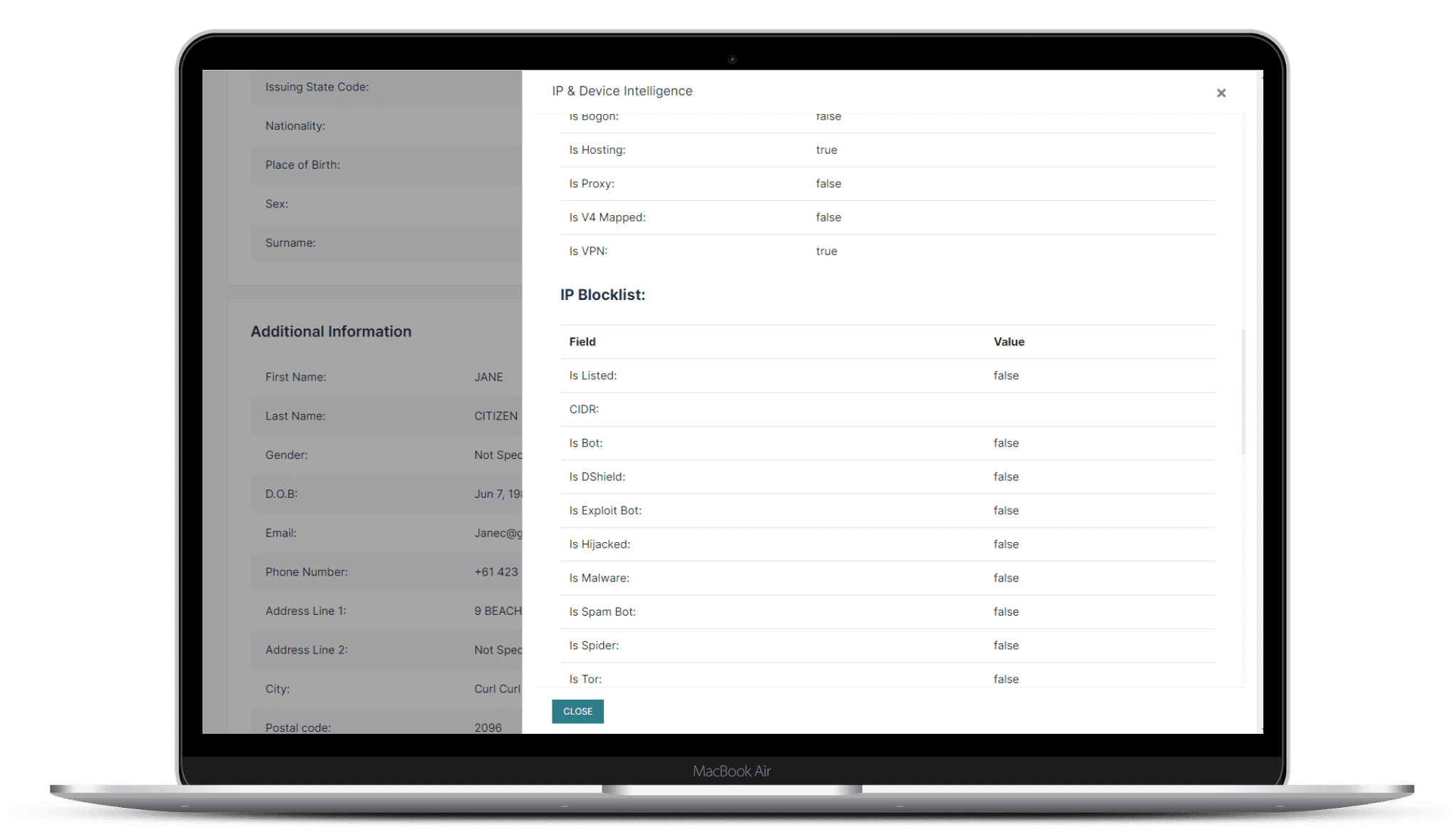
IP blocklist
Detect potentially malicious or dangerous IP addresses
ScreenlyyID will run an IP blocklist check to identify malicious hosts, anonymous proxies, tor, botnets, spammers and more.
Block, filter or flag traffic to help reduce attacks on your networks and software stacks.
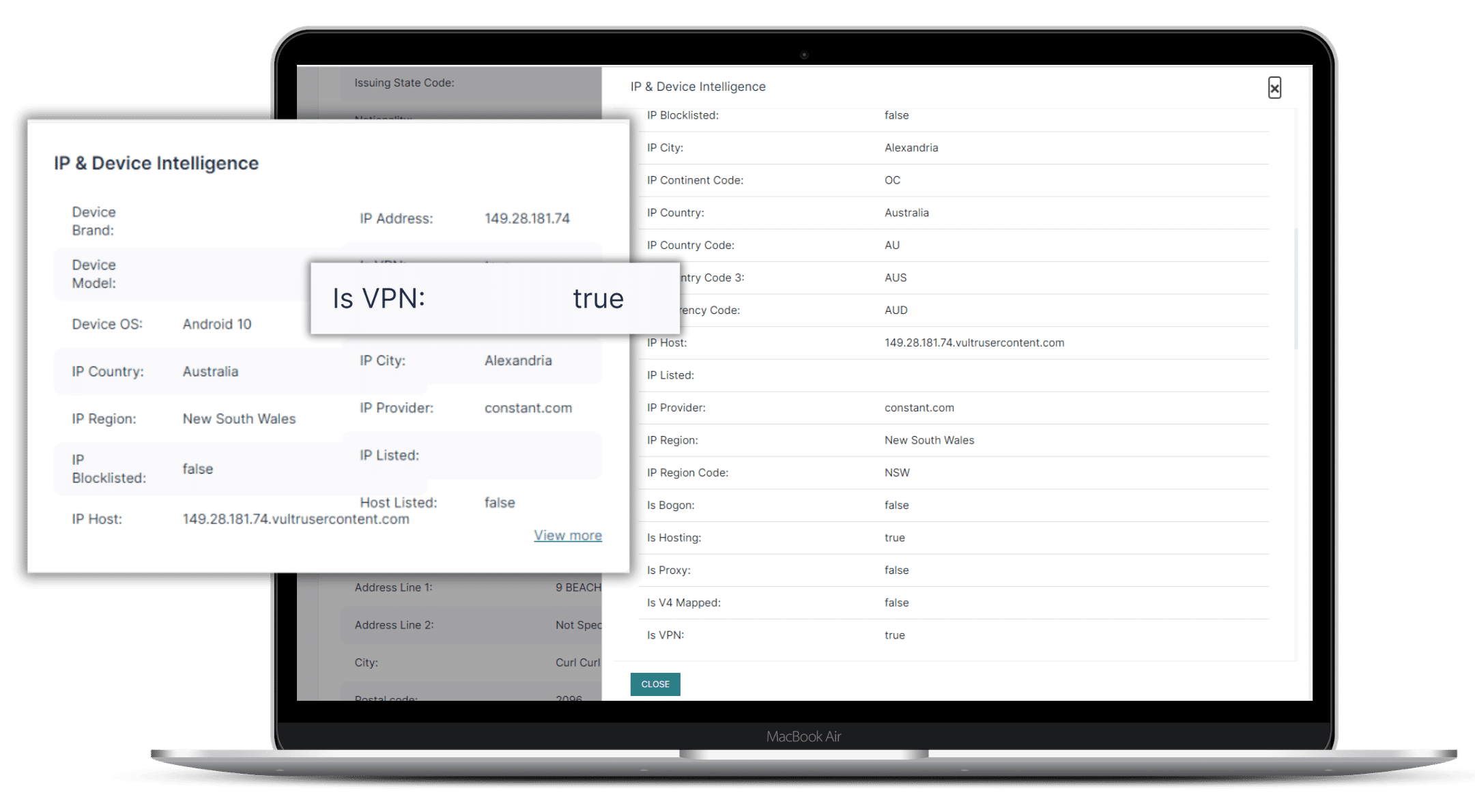
IP lookup provides detailed insights into a user's connection, covering VPN/proxy usage, Tor connections and more. Enhancing risk assessments, evaluating VPN/Tor users, and informing models for KYC, AML processes, iGaming bonus abuse, chargeback prevention, and beyond.
Identify dangerous IP's
Detect potentially malicious or dangerous IP addresses
ScreenlyyID will run an IP blocklist check to identify malicious hosts, anonymous proxies, tor, botnets, spammers and more.
Block, filter or flag traffic to help reduce attacks on your networks and software stacks.
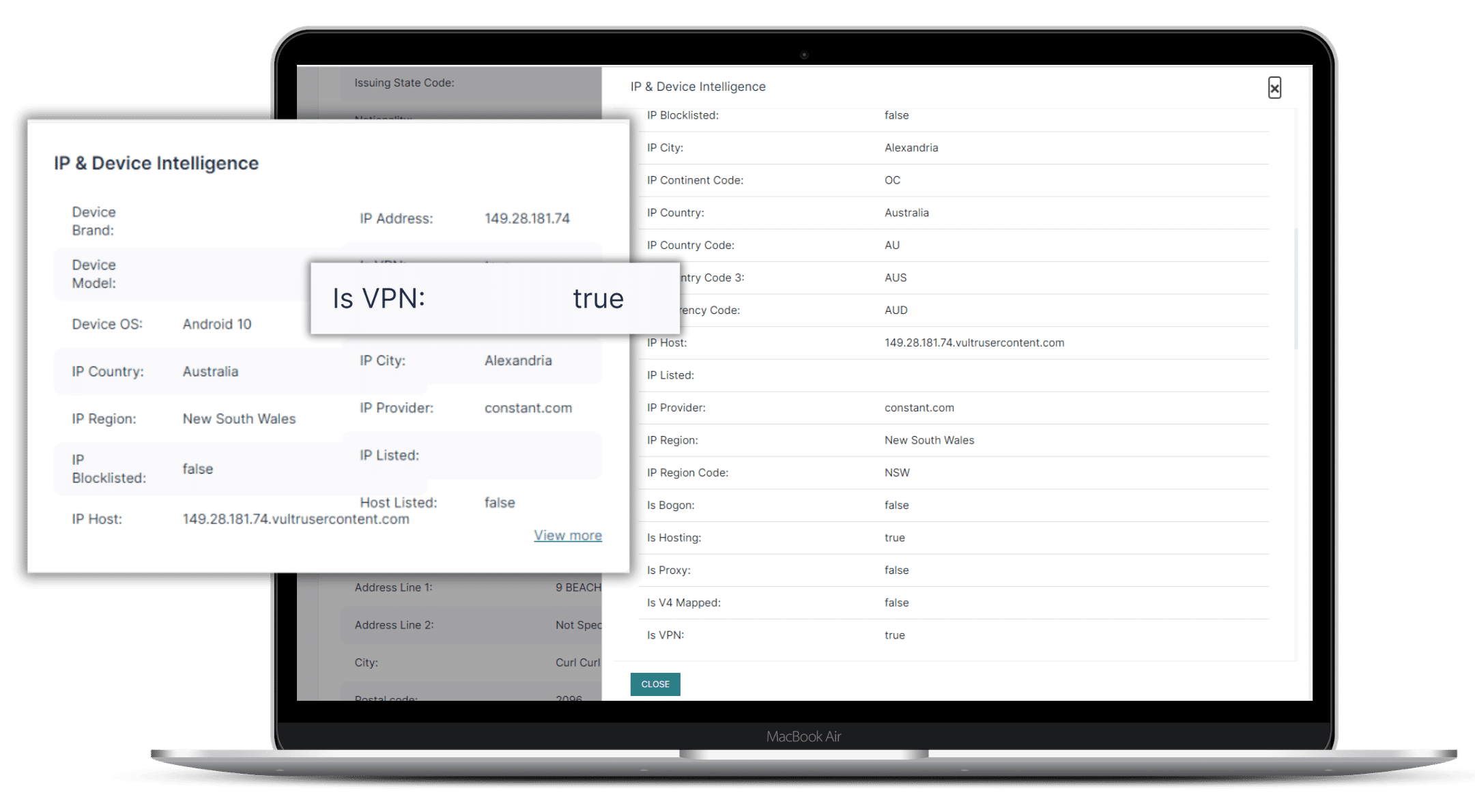
Identify suspicious proxies and VPN's
We look for the following
Identify the geolocation of an IP address down to the city level, including the geographic coordinates and detailed locale information. Our geolocation database is continuously updated in real time as internet address allocation changes and as new IP ranges come online.
IP blocklist will detect the following main categories of IP addresses:
- Open Proxies
- Tor nodes
- Public VPN's
- Spam hosts
- Phishing hosts
- Malware servers
- Attack sources
- Criminal netblocks
- Malicious spiders
- Bots and botnets
- Exploit scanners
- Brute-force crackers
Host Reputation
Identify high risk device IDs
ScreenlyyID will check the reputation of an IP address, domain name or URL against a comprehensive list of blacklists and blocklists to discern high risk device IDs. Under the hood there are three core blocklist components.
Autonomous Networks
Autonomous bots, crawlers and honeypots which continuously collect data from across the Internet in real time.
Protect against identity theft
Firewall Aggregation
Open Data
We compile data from many public sources of IP data, including public blocklists, blacklists, botnet trackers and various security intelligence feeds.
Assess the risk level of each new user
Combat fraudulent users on a large scale
Evaluate digital characteristics spanning phone, email, and IP data sets to promptly permit, block, or flag new registrations in milliseconds.

real-time digital identity and behavioral risk indicators
Instantly validate new identities
Ensure verification with certainty. Incorporate real-time digital identity and behavioral risk indicators into registration processes. Identify synthetic identities and enhance Know Your Customer (KYC) verifications without heightening user friction.

Prevent misuse of promotions
Close promo abuse loopholes
Combat multiple account creations to eliminate coupon misuse, exploit free trial gaps, and prevent referral fraud. Recapture revenue and reduce customer acquisition expenses.

Stop fraud in it's tracks
ScreenlyyID will help your organization eliminate all fraud related threats
Identity Theft
Account Takeover
Regulatory Fines
Money Laundering
Synthetic Identity
Phishing Attacks
Bot Attacks
Payment Disputes
Verification to suit your requirements
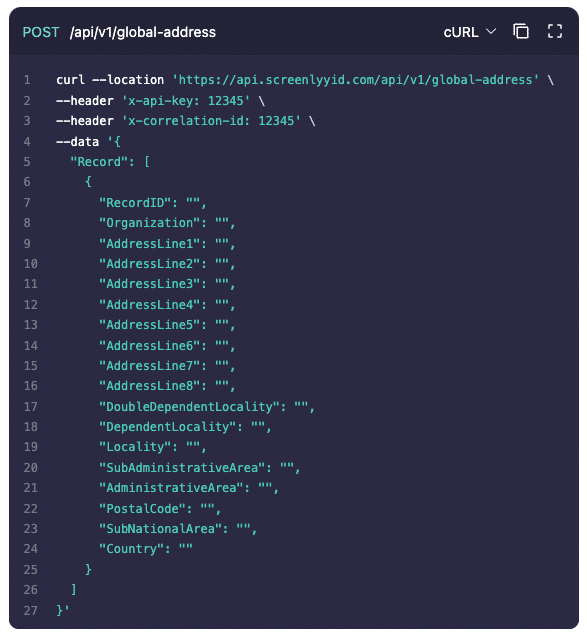
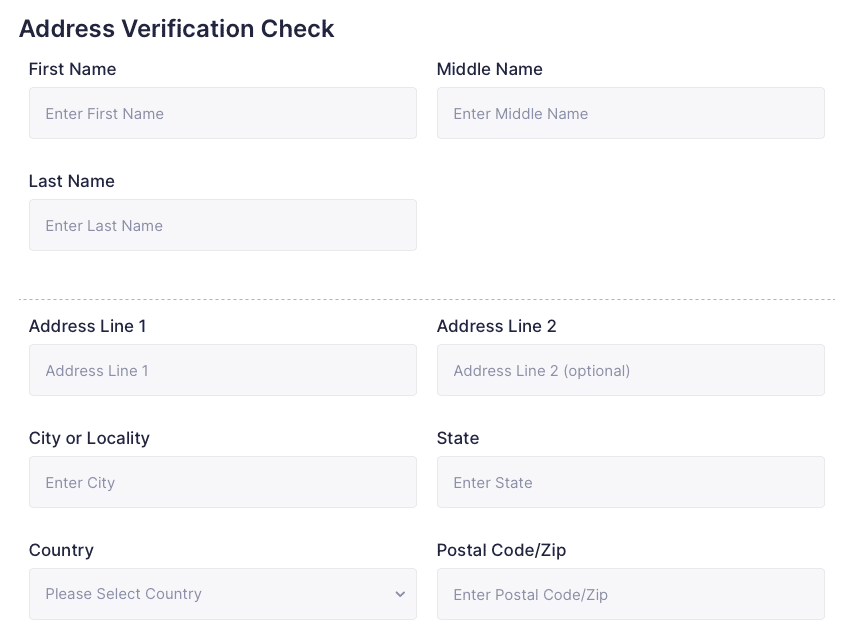
No-Code, Bulk CSV, API, or live lookup, we’ve got you covered
Competitive Pricing
Our pricing is the most flexible and affordable on the market
No Set Up Fee
No License Fee
Free Forever
No Hosting Fee
Contact us
Talk to an expert
Let’s connect to discuss the possibilities and find the perfect solution for your business needs.
Complete the form, and one of our experts will reach out to you. You’ll discover how our solutions can tackle your specific challenges, optimize your operations, and drive your growth.
- Explore industry-specific use cases
- Get pricing details
- Identify the best solution for you
